Master in Cyber Security Law and Policy
Gain hands-on skills to detect, secure, and remediate cyber threats, master forensics, and implement legal, technical, and strategic cybersecurity solutions.
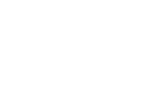
#1 Most Popular Online Course & Internship in Law You can enroll today & get certified from EasyShiksha & HawksCode.

Why This Course and Internship Stands Out
See exactly what separates EasyShiksha students from everyone else
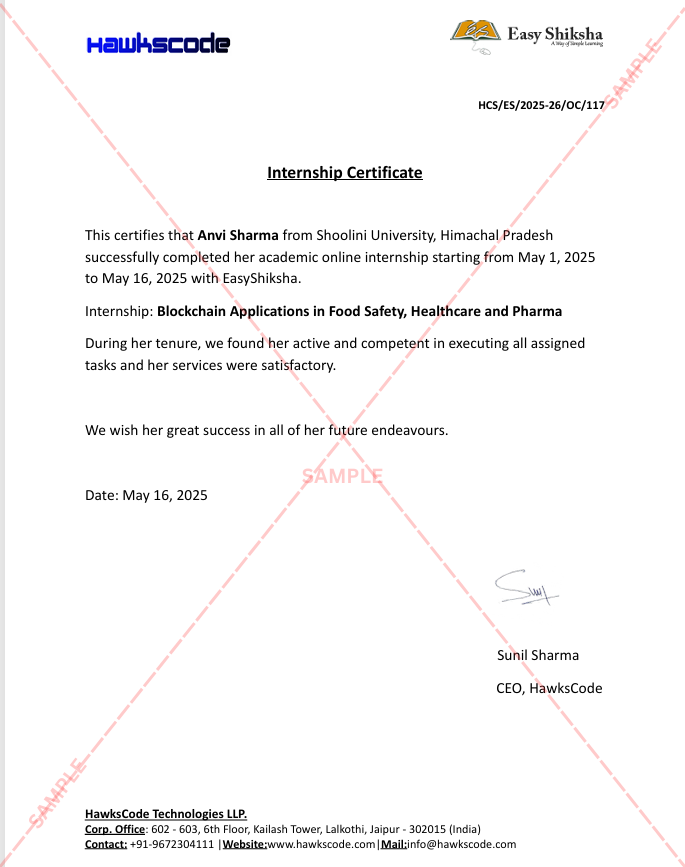
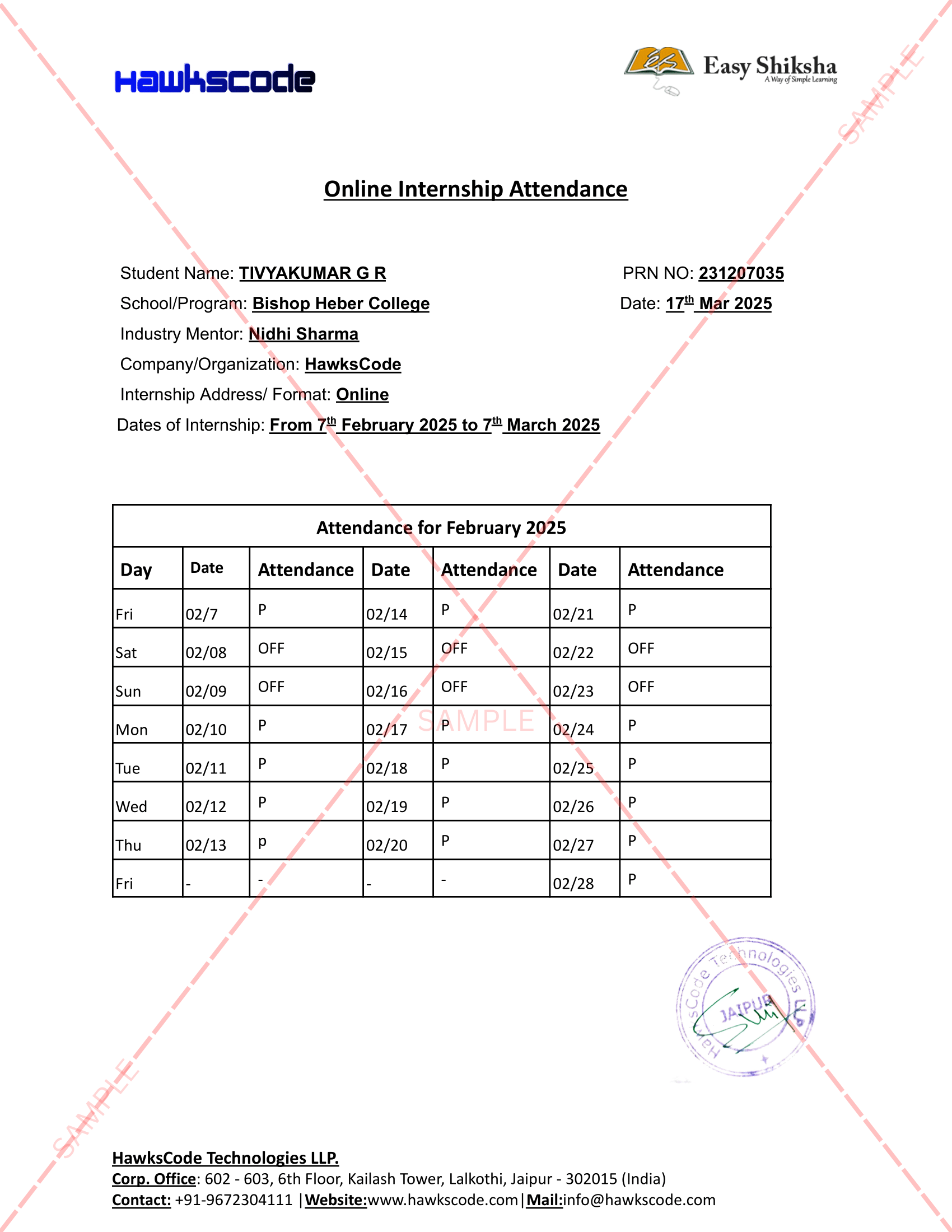
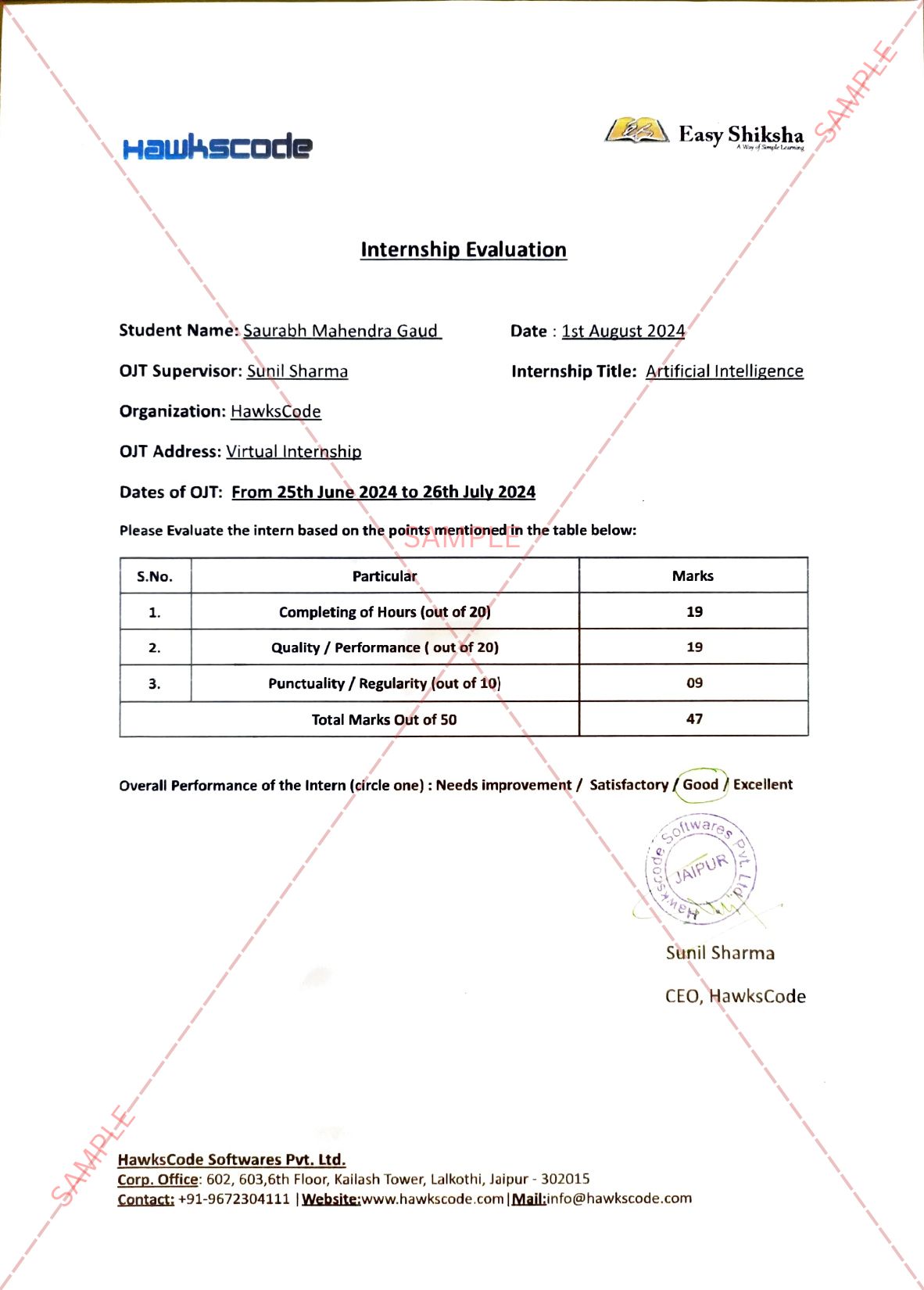
Internship Opportunity Included With This Course
"This is not just a course — it's real career experience. Walk away with documents that prove your skills to any employer."
This Course is Perfect For
Whether you're starting from scratch or switching careers — this course is designed with your success in mind.
The course is designed in a way that a candidate can identify, analyze and remediate computer safety breaches by way of gaining knowledge of and imposing the actual-world eventualities in Cyber Investigations Laboratory, community protection Laboratory and in security and Penetration testing Laboratory and also about Information technology act .This course also highlights about the legal issues taking place and cyberspace and also about E-contracts.
❖ Showcase expertise to cozy corrupted structures, guard personal information, and relaxed computer networks in an organization.
❖ Practice with an understanding in lecturers to design and enforce safety answers.
❖ Apprehend key phrases and ideas in Cryptography, Governance and Compliance.
❖ Broaden cyber protection techniques and policies
❖ Understand standards of web security and to guarantee a comfortable community by means of monitoring and studying the character of assaults via cyber/pc forensics software/tools.
❖ Upon a hit crowning glory of the programme, candidates might be acquainted with cyber protection landscapes and capable of
A) Examine and compare the cyber safety wishes of a corporation.
B) Determine and analyze software program vulnerabilities and protection answers to reduce the risk of exploitation.
C) Degree the performance and troubleshoot cyber safety structures.
D) Put into effect cyber security solutions and use of cyber protection, facts assurance, and cyber/computer forensics software program/gear.
E) Recognize and execute danger control strategies, danger remedy strategies, and key risk and overall performance signs
F) Layout and increase a protection architecture for an enterprise.
g) Layout operational and strategic cyber security strategies and rules.
Module 1- Analysis to Cyber Law and Cyber Space.
A) Definition and Nature of Cyber Space.
B) Difference between Crime and Cyber Crime.
C) Nature of Cyber Law vis-a-vis IT Act
D) Scope of IT Act.
Module 2- Overview of E-Contracts
A) E-Commerce vis-avis E-Contracts - Nature and Scope
B) Legal Issues in E-Contracts.
C) E-Contracts - Enforceability and Privacy Issues
D) Introduction to Digital Signature
Module 3- Cyber Space vis-a-vis Intellectual Property Rights
A) Cyber Space vis-a-vis Trademark
B) Cyber Space vis-a-vis Copyright
C) Copyright Infringement - Scope
D) Doctrine of Fair Dealing
Module 4- Introduction to Cyber Crimes
A) Cyber Crimes - Nature and its Types
B) Cyber Crimes in International Scenario
C) Cyber Crimes in Indian Scenario.
D) Cyber Activism – Nature
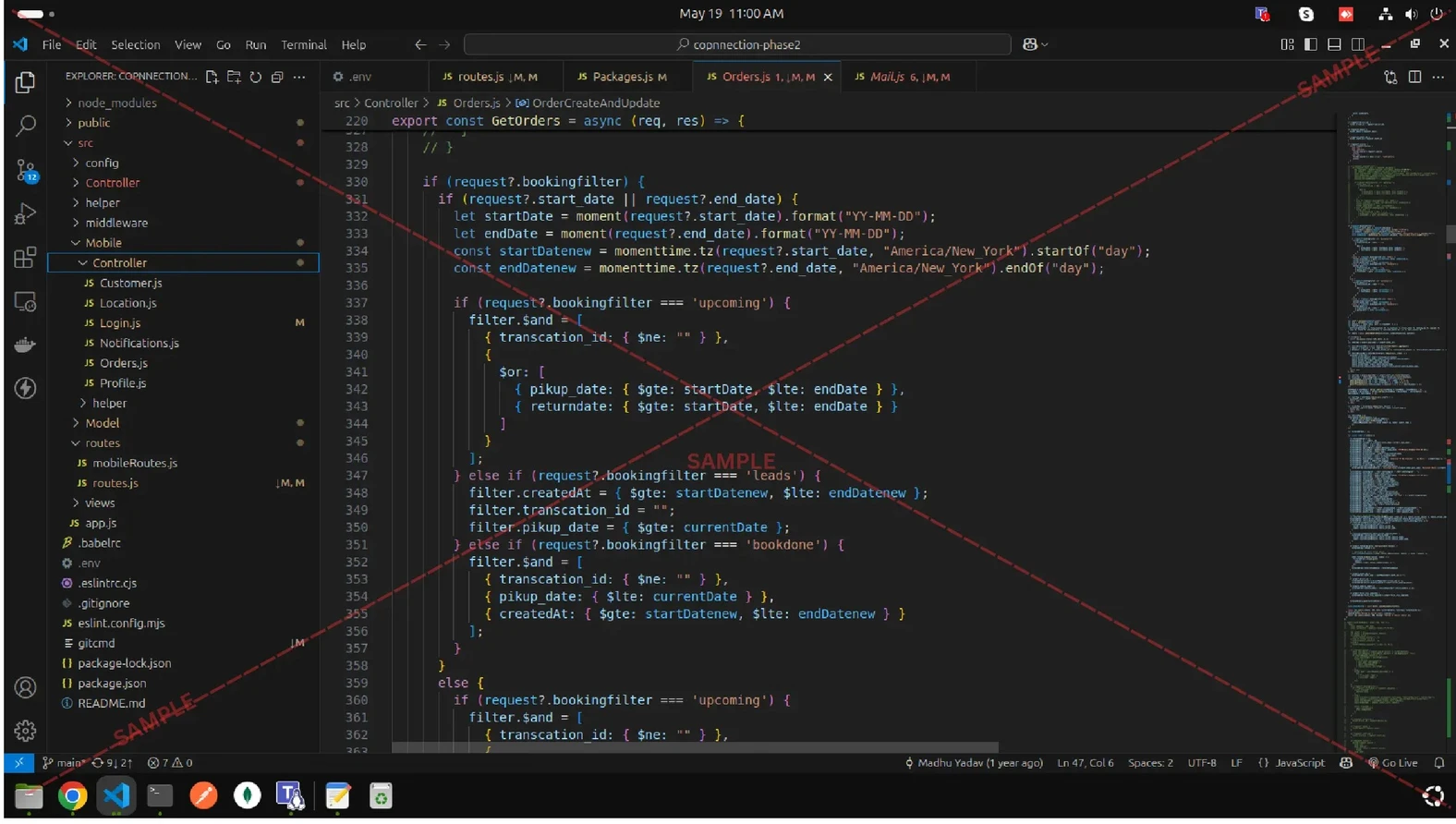
Step-by-step instructions are very easy to follow
Why Start Now?
The Opportunity Won’t Wait.
Every day you delay is a missed opportunity to grow your skills. Learners who start today gain the advantage — whether it's building skills, improving careers, or unlocking new opportunities.
Still Thinking?
Here's everything that makes this a no-brainer:
What Happens After You Enroll?
From payment to certificate — here's exactly what to expect
Imagine After Completing This Course
Picture yourself 30 days from now — with skills, experience, and credentials that open real doors.
























Shoaib Baloch
-
02 Dec 2024Step-by-step instructions are very easy to follow