Enterprise Endpoint Governance, Lifecycle, and Control Mastery
Master enterprise endpoint governance and lifecycle management to secure assets, ensure compliance, optimize operations, and lead IT transformation.
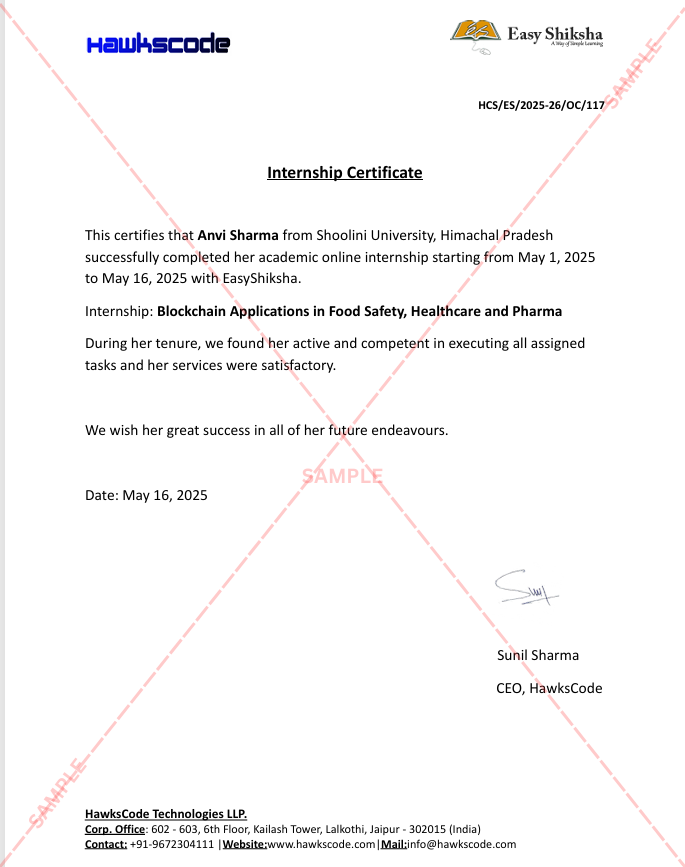
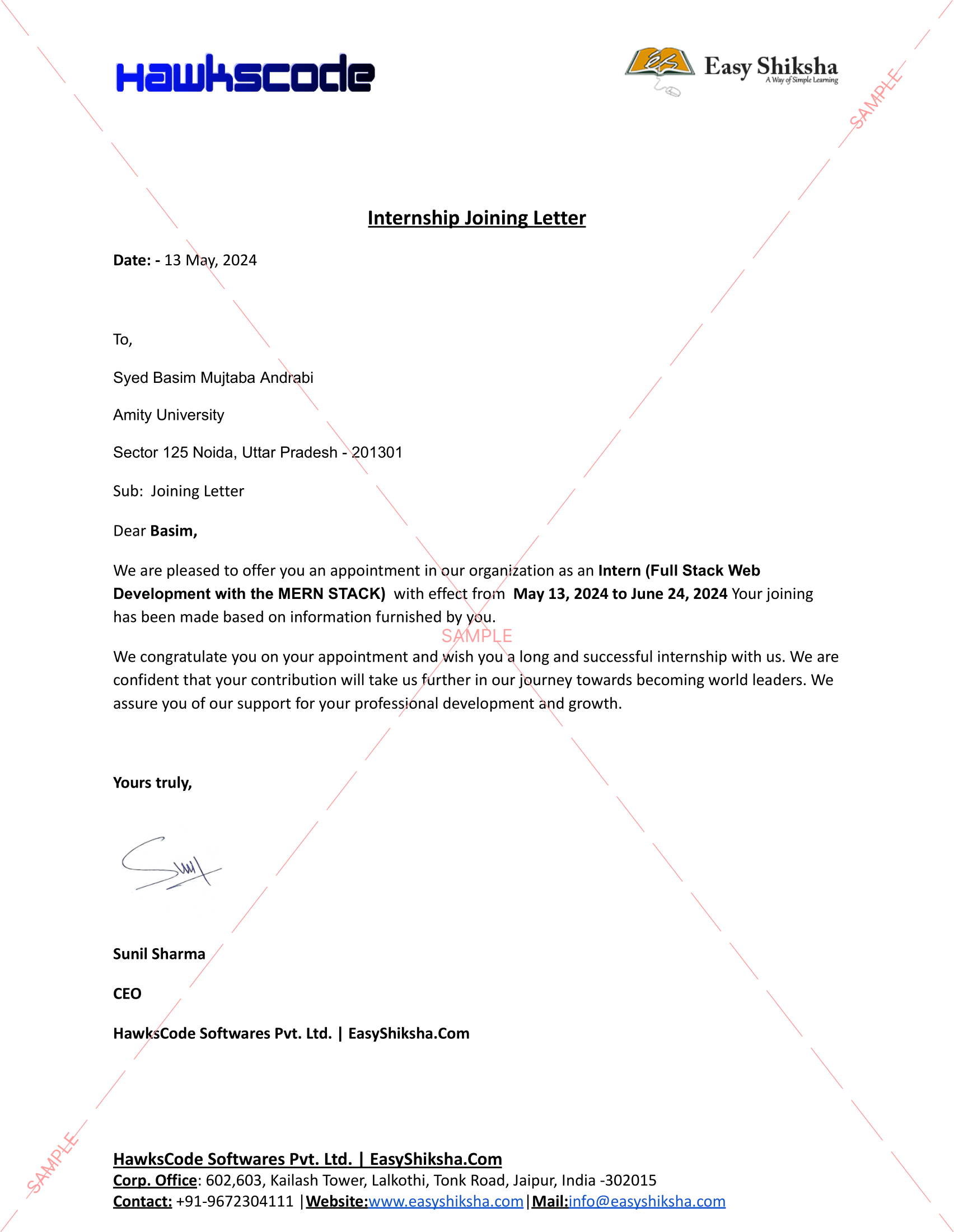
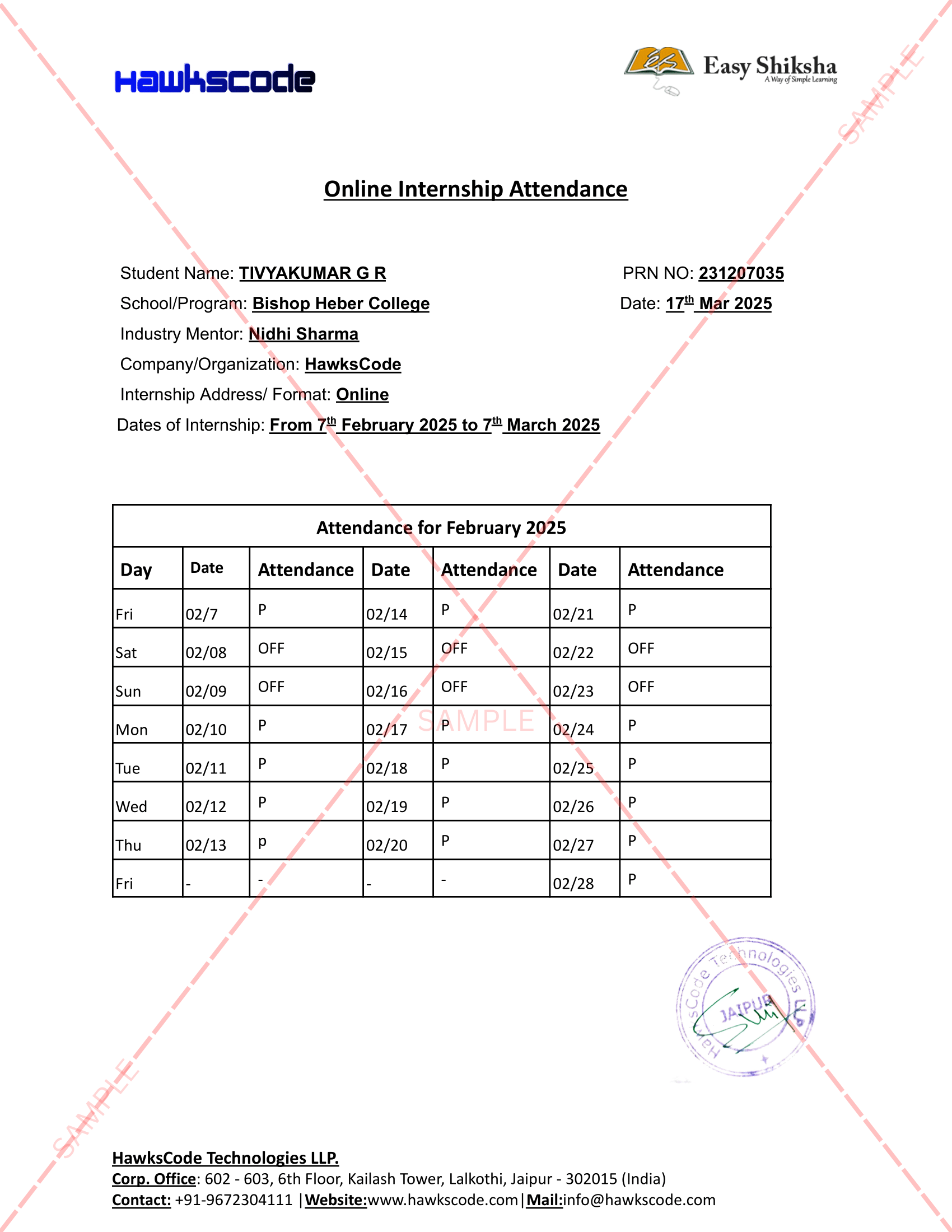
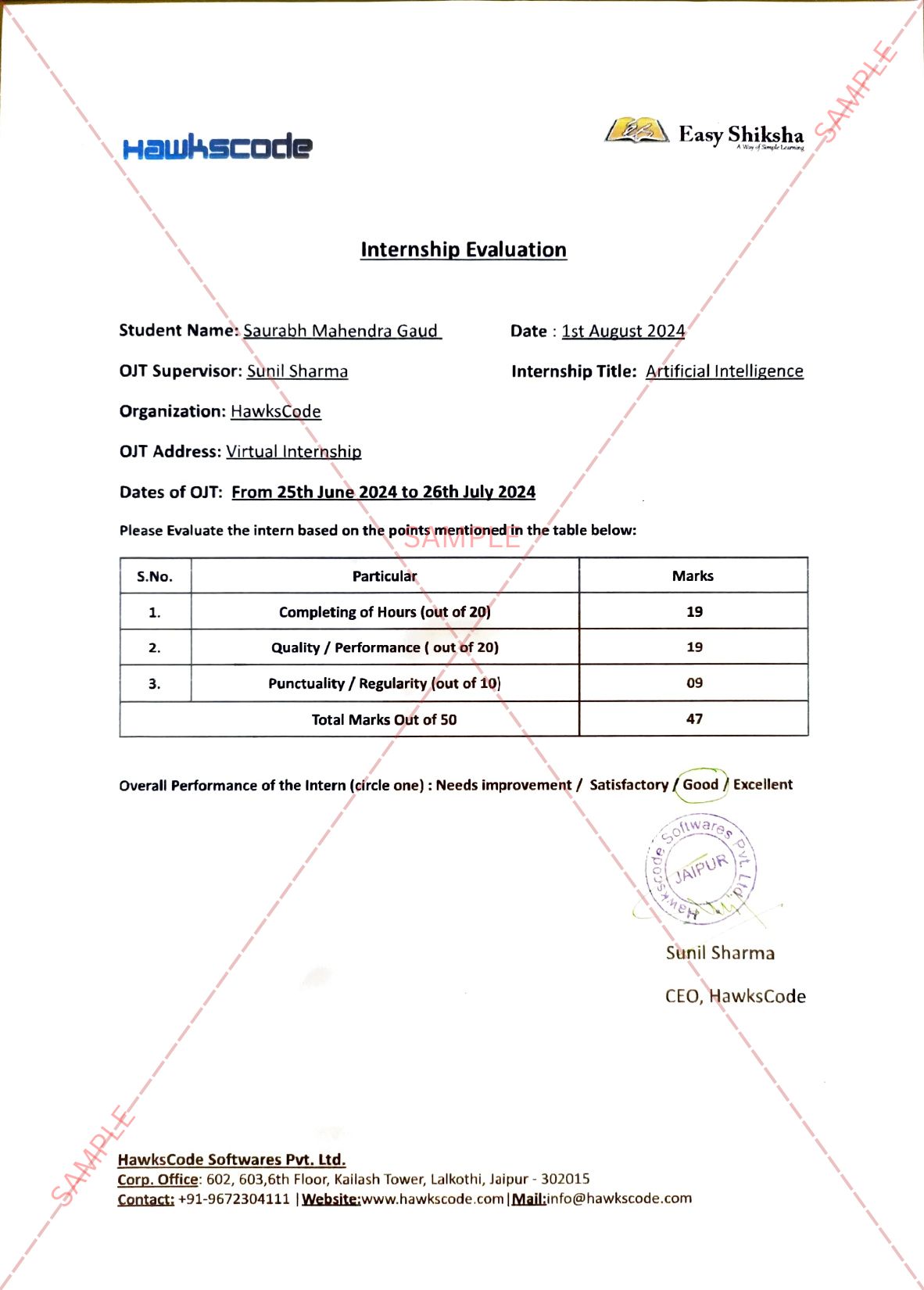
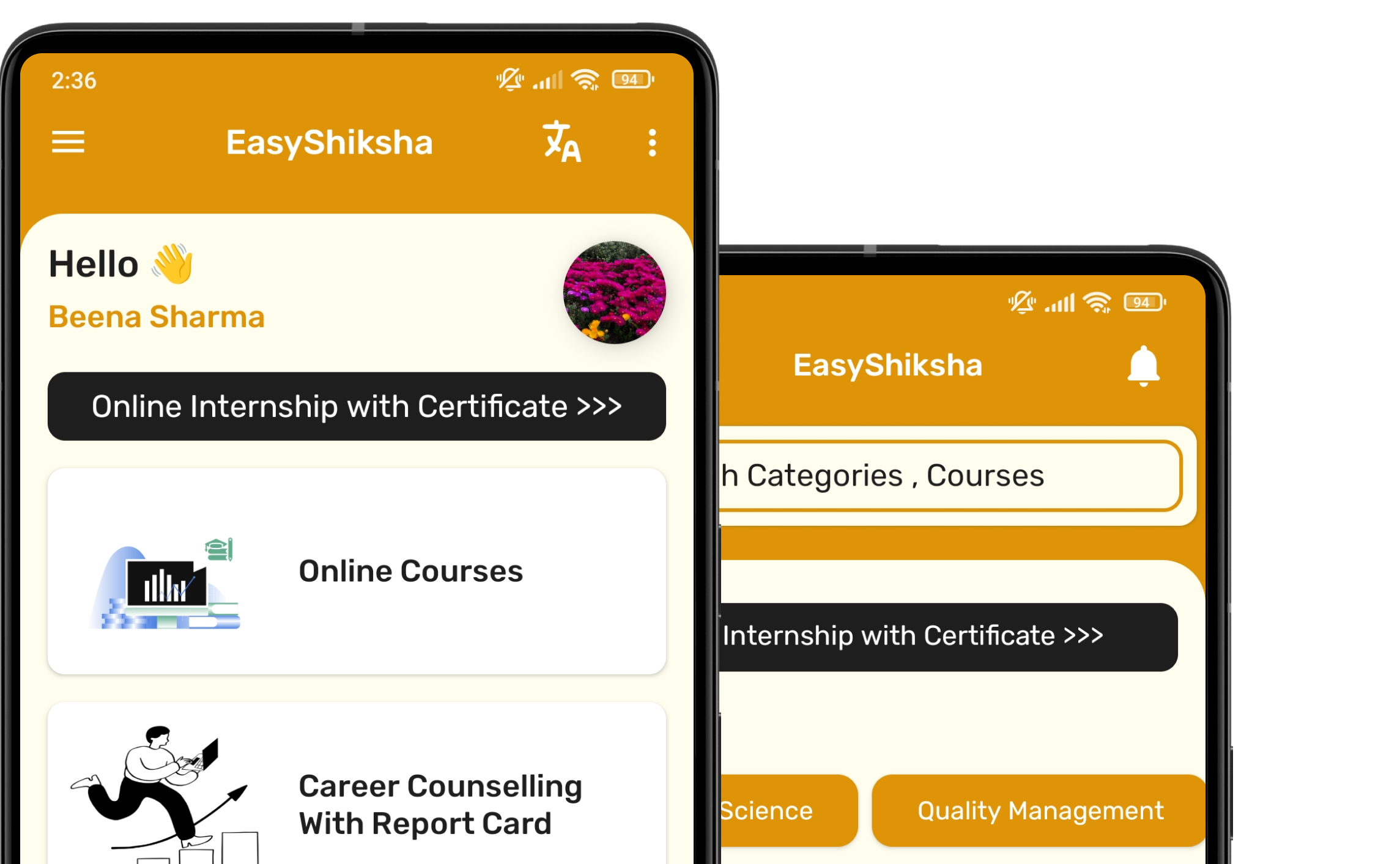
#1 Most Popular Online Course & Internship in Engineering You can enroll today & get certified from EasyShiksha & HawksCode.

Why This Course and Internship Stands Out
See exactly what separates EasyShiksha students from everyone else
Internship Opportunity Included With This Course
"This is not just a course — it's real career experience. Walk away with documents that prove your skills to any employer."
This Course is Perfect For
Whether you're starting from scratch or switching careers — this course is designed with your success in mind.
This course uses elements of Artificial IntelligenceAre you ready to become an enterprise IT leader—someone who doesn’t just manage endpoints, but masters the systems that shape the security, compliance, and efficiency of your entire organization? In modern enterprises, the digital landscape is vast, complex, and in constant flux. Recent studies show that nearly 70% of cybersecurity breaches stem from poor endpoint management, while globally, regulatory and audit failures cost organizations billions of dollars each year. Yet, for those who invest in strong endpoint governance and lifecycle management, the payoff is measurable: lower legal risk, stronger security postures, better operational agility, and a tech environment that empowers rather than disrupts. This is your chance to gain the skills and insights that define the most trusted IT strategists.
Our team is comprised of seasoned enterprise architects, compliance leaders, and endpoint governance specialists who have led global deployments and IT transformations for Fortune 500 organizations and public sector institutions alike. We know first-hand the pain of fragmented device ownership, the rescue missions after high-profile security incidents, and the cost-saving power of well-designed policies and processes. Drawing from these deep experiences—hard-won victories and lessons learned—we built this course not just for knowledge transfer, but to equip you with immediately actionable strategies and a portfolio of best practices that will distinguish your expertise in any organization.
Today’s enterprise IT professionals face unprecedented challenges: rapidly evolving regulatory requirements, remote and hybrid workforces, and a technological ecosystem that now includes everything from traditional PCs to IoT and cloud-native devices. Without robust endpoint governance, the risks multiply—data breaches, failed audits, operational inefficiencies, and a proliferation of technical debt that can paralyze innovation. Yet, with the right approach to device control, configuration, audit, and lifecycle management, organizations can turn their digital environments into pillars of security, compliance, and business agility. Our course is your toolkit for this transformation, whether you’re modernizing legacy fleets, merging organizations, or preparing for the next leap in digital evolution.
Throughout this journey, you’ll experience a seamless blend of conceptual mastery and practical implementation. The course opens by demystifying endpoint governance—exploring not just what it is, but why it is the bedrock of effective IT management in the enterprise. You’ll journey through the evolution of System Center Configuration as the backbone of enterprise policy and learn how governance provides the strategic framework to maximize its impact. Historical and real-world case studies will immerse you in authentic, high-stakes environments, as we dissect both the pitfalls of weak governance and the triumphs of robust, proactive control.
Next, you’ll be immersed in the nuanced art of policy enforcement. What does it take to design, implement, and sustain policies that ensure uniform security and compliance across thousands, or even hundreds of thousands, of devices? From centralized and decentralized control models to the balancing act between organizational requirements and user flexibility, we draw on direct experience from global enterprises to show how even the most entrenched policy conflicts can be resolved with intelligence and sensitivity. You'll analyze real incidents where policy breakdown led to vulnerabilities, and contrast them with successes where governance directly prevented security breaches and costly incidents.
Security, always a top priority, takes center stage as we guide you through the implementation of enforceable security baselines, the use of centralized policies to prevent breach scenarios, and the utility of incident response protocols that leverage governance infrastructures. You’ll study case histories where strong governance either prevented or failed to mitigate high-visibility security events—learning how decisions before an incident predict long-term outcomes.
Of course, compliance isn’t optional in today’s regulatory landscape—so we dedicate significant focus to translating legal, regulatory, and internal policy requirements into concrete, auditable governance practices. You’ll map frameworks such as GDPR, HIPAA, and SOX to technical controls, learn how to prepare evidence-ready documentation and reporting, and see industry examples where System Center became the linchpin for passing audits and reducing organizational risk. Assessments will challenge you to create compliance maps and reporting templates for real and hypothetical organizations, giving you portfolio-ready examples and hands-on experience.
Operational efficiency is more than an aspiration—it’s a necessity for IT’s strategic role. You’ll discover how centralized endpoint governance eliminates redundancy, unlocks cost efficiencies, and streamlines service delivery, especially for support and helpdesk operations. We provide methodologies and workflow templates developed in enterprise environments, and challenge you to optimize real-world scenarios for maximum operational health.
Diving deeper, we introduce the concept of enterprise endpoint lifecycle management—the discipline of strategically planning, provisioning, updating, monitoring, and retiring devices for minimal technical debt and maximum compliance. Through interactive modules and project-based learning, you’ll craft lifecycle management strategies for organizations of varying sizes and regulatory complexity, learning how provisioning with gold images, standardized baselines, and merger-ready practices can make or break organizational technology transitions. You’ll explore the full lifecycle, from device onboarding to secure end-of-life disposal, grounded in case studies both triumphant and cautionary.
Patching and update management are dynamic and sometimes precarious balancing acts. You’ll master frameworks for consistent, scalable patch lifecycle control—analyzing real-life incidents triggered by poor patch management and planning update strategies that meet both urgent and stability needs. Our hands-on assessments will have you design patch management plans for complex environments, demonstrating readiness to handle everything from zero-day vulnerabilities to compliance-driven audits.
A critical differentiator of this course is our full lifecycle approach to operational health: proactive monitoring, automated alerting, and the use of historical device health baselines to catch emerging problems before they disrupt business. We share proven monitoring workflows, alert strategies, and incident response practices from our own enterprise consulting experiences—then challenge you to architect monitoring and alerting plans that could save millions by preventing device-wide failures and data loss.
No course on enterprise endpoint management is complete without rigorous instruction on device retirement and replacement. You'll learn not just how to identify devices ready for decommissioning, but how to minimize the associated data and compliance risks—including sustainable, environmentally responsible disposal strategies. We supplement our frameworks with detailed failure analyses and case studies, showing how improper device retirement has resulted in regulatory and reputational crises.
Managing technical debt and operational fragmentation often separates high-performing IT teams from the rest. We go beyond the basics to help you identify, prioritize, and schedule long-term upgrades, teaching through stories of environments weighed down by legacy systems and disjointed management tools. Our recovery narratives and consolidation strategies are drawn from large-scale rescue projects and mergers—providing playbooks to transform technical debt into future-ready infrastructure.
Control and accountability are essential elements under our lens. We guide you in defining accountability within sprawling IT estates, balancing between the necessity of central control and the flexibility of delegated operational authority. Leveraging the audit and documentation capabilities of System Center, you’ll learn to design and implement transparent, traceable environments where every decision leaves a trusted record—an asset both for forensic investigations and regulatory peace of mind.
Central to the value of our course is an honest, practical examination of trade-offs: When should you prioritize organizational flexibility over control, or vice versa? Using case studies from creative, research, and highly regulated departments, you’ll develop frameworks to weigh the impact of control on innovation, productivity, and risk.
Audit, documentation, and evidence aren’t mere compliance checkboxes—they are tools for building trust and accountability throughout the enterprise. We’ll teach you principles for maintaining airtight audit trails, documenting every policy, configuration, and change, and using audit logs as powerful evidence in both everyday troubleshooting and major compliance or security incidents.
As enterprises become more heterogeneous—spanning different device OEMs, operating systems, and work models (including hybrid, remote, and BYOD)—we prepare you to standardize operations without stifling diversity. Our content addresses the real-world complexities faced by multinational organizations, equipping you with approaches to cross-platform policy enforcement and operations that serve evolving workforce models, including lessons learned from the abrupt, global shift to remote work during the COVID-19 pandemic.
Looking ahead, we help you future-proof your governance frameworks. As Internet of Things, edge devices, mobile endpoints, and AI-driven automation reshape enterprise technology, you’ll discover how to adapt your policies and controls seamlessly. We blend thought leadership with practical, real-world readiness, preparing you not only to respond but to anticipate the needs of the next generation of enterprise endpoint management.
Throughout the course, you’ll complete hands-on projects, from mapping governance requirements to real environments, architecting compliance-driven provisioning workflows, and establishing robust monitoring and audit frameworks. Assessment tools and peer feedback ensure not only knowledge retention, but the ongoing development of a portfolio that will elevate your professional profile—whether in job interviews, audits, or boardroom presentations.
What sets this course apart? Our unique blend of theory and practice, experienced instructor team, and deep integration of real-world, high-stakes scenarios. We deliver the most up-to-date, enterprise-tested approaches to endpoint governance, lifecycle management, compliance, auditing, incident response, and operational efficiency, preparing you for the complexities and opportunities of today’s—and tomorrow’s—enterprise IT.
If you’re ready to become the IT professional who leads transformation—not just manages chaos—enroll now. Equip yourself with the strategies, frameworks, and evidence-driven practices that drive security, compliance, operational excellence, and innovation in the world’s most complex organizations. Step into the future of enterprise endpoint governance with us. Your path to strategic IT mastery begins here.
Why Start Now?
The Opportunity Won’t Wait.
Every day you delay is a missed opportunity to grow your skills. Learners who start today gain the advantage — whether it's building skills, improving careers, or unlocking new opportunities.
Still Thinking?
Here's everything that makes this a no-brainer:
What Happens After You Enroll?
From payment to certificate — here's exactly what to expect
Imagine After Completing This Course
Picture yourself 30 days from now — with skills, experience, and credentials that open real doors.