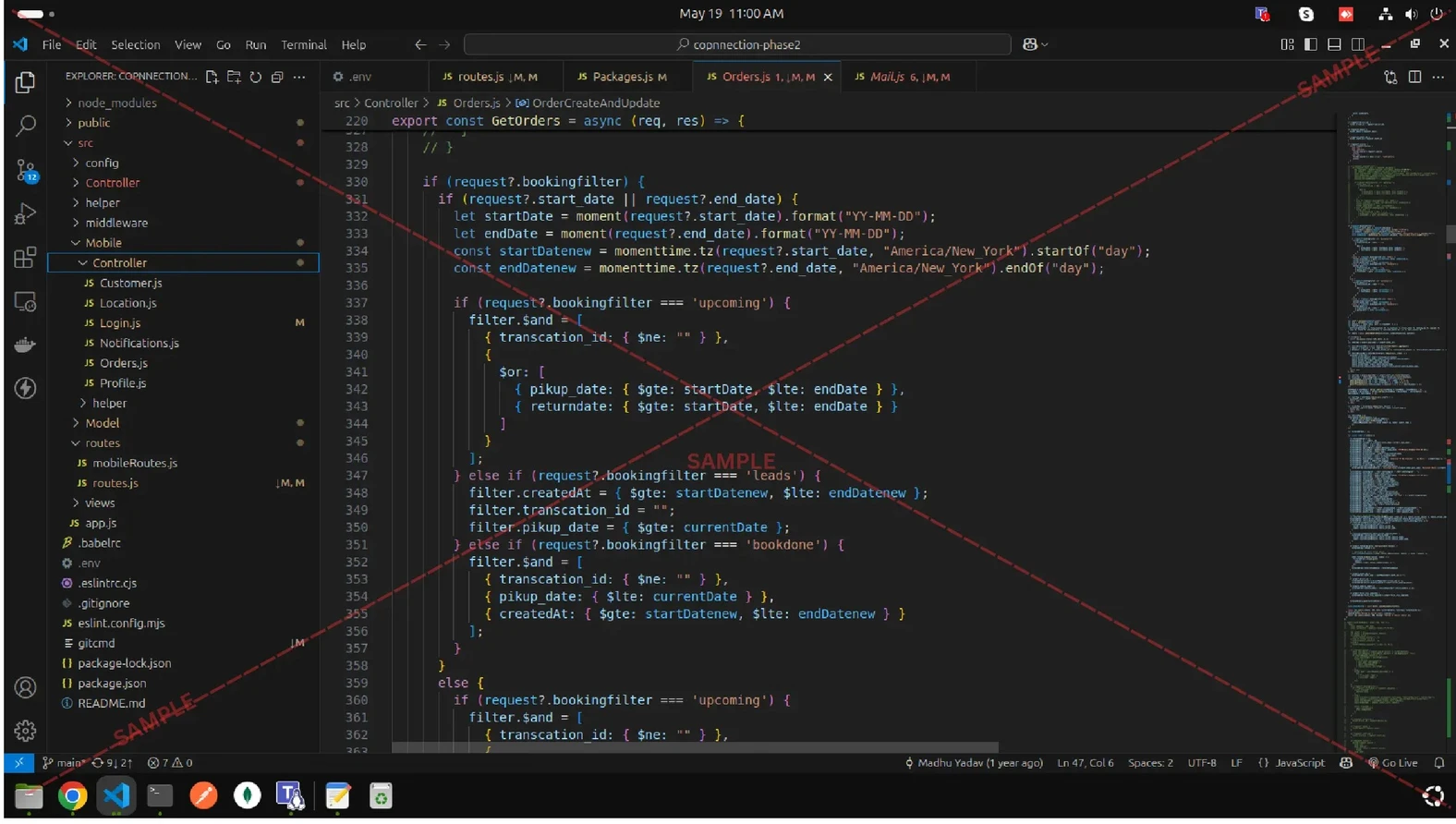
Why Hackers Target Websites and How They Do It
Master the hacker mindset to identify vulnerabilities, counter cyber attacks, and secure websites against real-world threats.
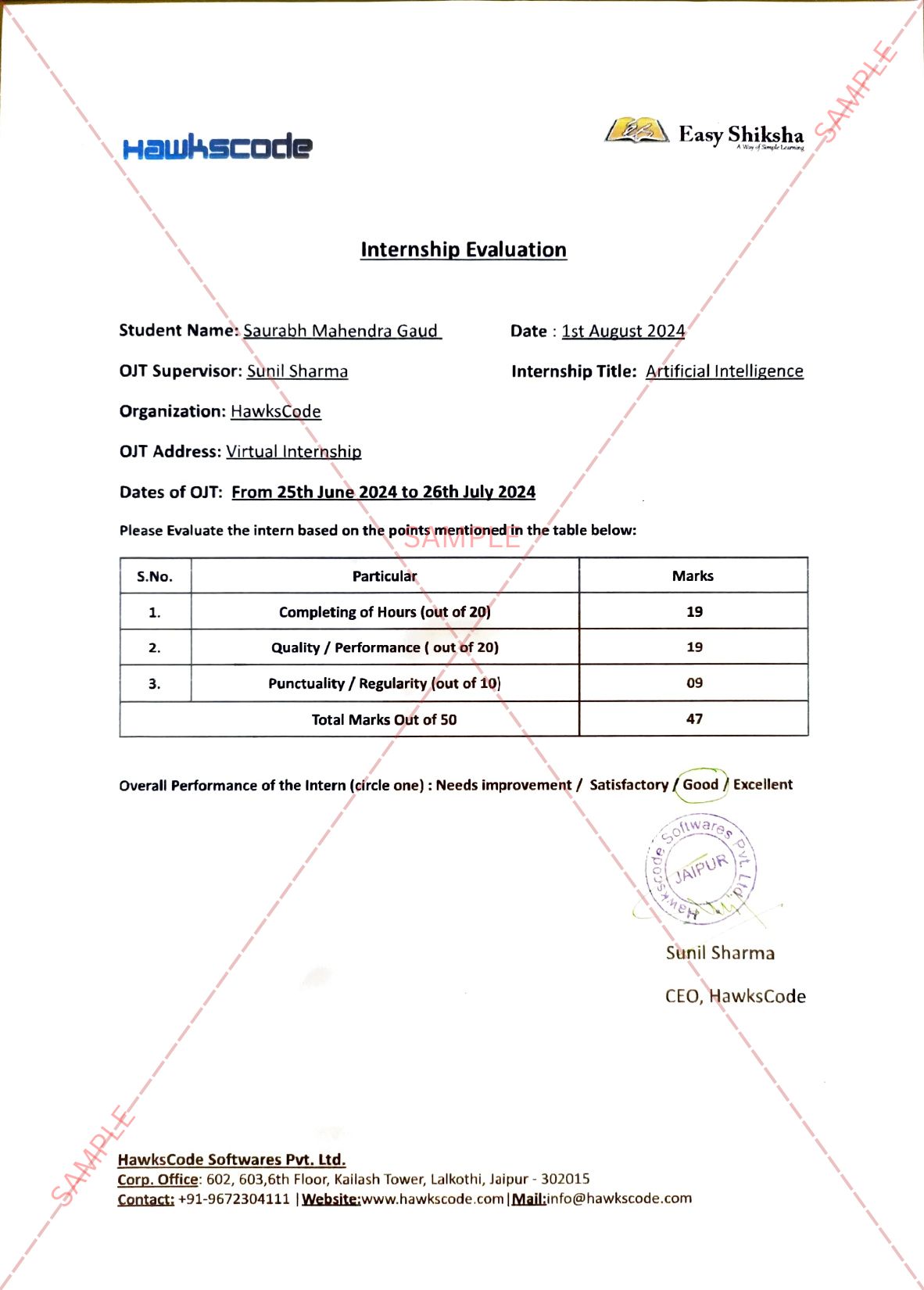
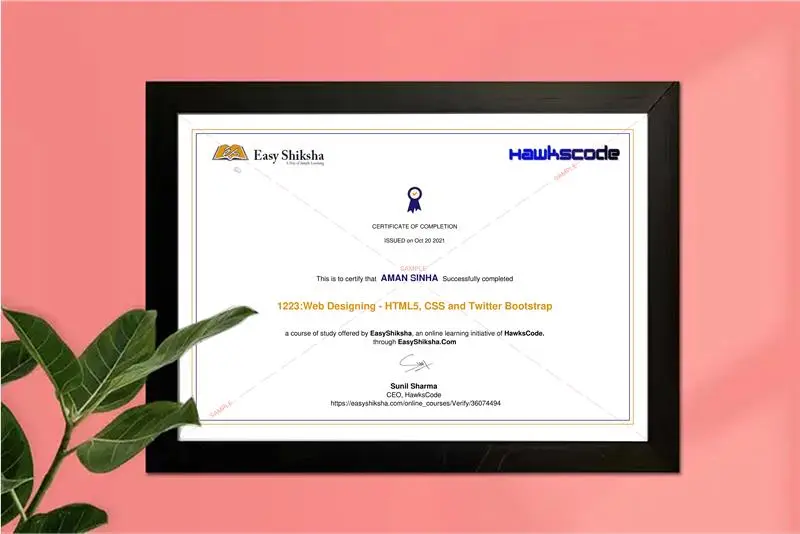
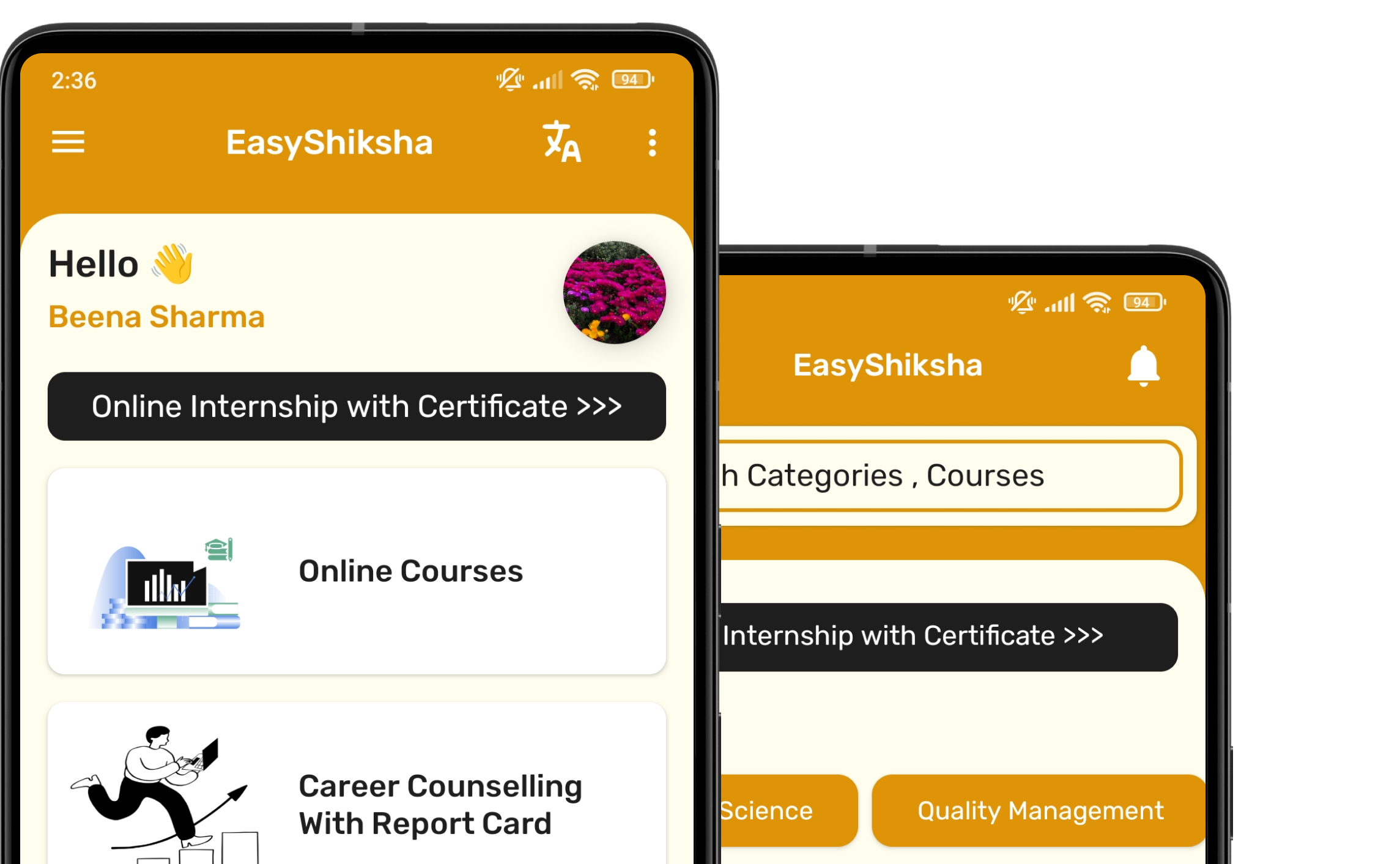
#1 Most Popular Online Course & Internship in Cyber Security You can enroll today & get certified from EasyShiksha & HawksCode.
Why This Course and Internship Stands Out
See exactly what separates EasyShiksha students from everyone else
Internship Opportunity Included With This Course
"This is not just a course — it's real career experience. Walk away with documents that prove your skills to any employer."
This Course is Perfect For
Whether you're starting from scratch or switching careers — this course is designed with your success in mind.
In today’s digital age, websites are prime targets for hackers due to their critical role in business, communication, and data storage. This course, Hackers vs. Websites: Motivations, Weaknesses, and Techniques, provides a comprehensive exploration of the motivations behind website attacks, the vulnerabilities hackers exploit, and the techniques they use to compromise websites. Whether you're a website owner, developer, cybersecurity enthusiast, or simply curious about the dark side of the internet, this course will equip you with the knowledge to understand and defend against cyber threats.
Key Topics Covered:
1. Motivations Behind Website Attacks:
Explore why hackers target websites, including financial gain, data misuse, personal revenge, fun, recognition, and hacktivism.
2. Common Weaknesses Exploited by Hackers:
Learn about vulnerabilities such as weak passwords, outdated software, and misconfigured servers that make websites easy targets.
3. Hacking Techniques:
Understand methods like brute force attacks, SQL injection, malware injection, supply chain attacks, and e-skimming.
4. Types of Cyber Attacks:
Dive into DoS and DDoS attacks, MITM (Man-in-the-Middle) attacks, and social engineering tactics like phishing, baiting, pretexting, and quid pro quo.
5. Impact of Attacks:
Analyse the financial and reputational costs of cyber-attacks, including ransomware, data breaches, and prolonged e-skimming.
6. Hacktivism and Cyber Espionage:
Discover the goals of hacktivists and how hackers are hired for corporate espionage or to disrupt competitors.
7. Spam and Its Role in Cyber Attacks:
Understand how spam emails or messages, though seemingly harmless, can be used as tools for phishing or malware distribution.
8. Real-World Examples and Case Studies:
Examine real-life incidents to understand how attacks are executed and their consequences.
By the end of this course, students will gain a deep understanding of the motivations driving hackers, the weaknesses they exploit, and the techniques they use to compromise websites. They will learn how to identify potential vulnerabilities, recognize common attack methods, and implement strategies to protect websites from cyber threats. This course is ideal for anyone looking to enhance their cybersecurity knowledge, safeguard their online presence, or pursue a career in cybersecurity. Join us to uncover the hidden world of hackers and learn how to defend against their ever-evolving tactics.
Why Start Now?
The Opportunity Won’t Wait.
Every day you delay is a missed opportunity to grow your skills. Learners who start today gain the advantage — whether it's building skills, improving careers, or unlocking new opportunities.
Still Thinking?
Here's everything that makes this a no-brainer:
What Happens After You Enroll?
From payment to certificate — here's exactly what to expect
Imagine After Completing This Course
Picture yourself 30 days from now — with skills, experience, and credentials that open real doors.