Mastering Enterprise Identity: Architecture, Security, Trust Models
Master enterprise identity architecture to design, defend, and govern secure, resilient systems, mitigating insider risks, breaches, and regulatory threats.
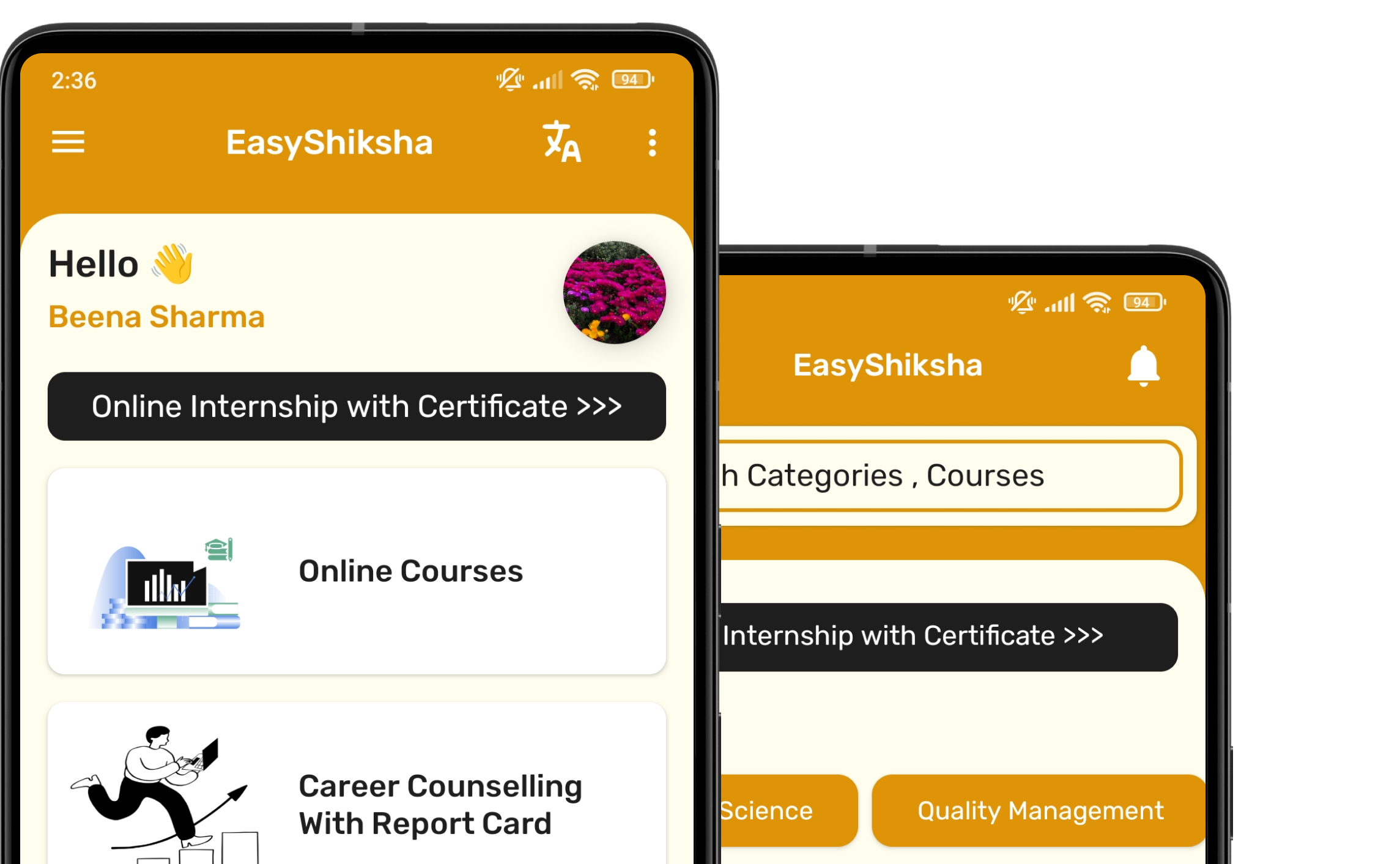
#1 Most Popular Online Course & Internship in Cyber Security You can enroll today & get certified from EasyShiksha & HawksCode.

Why This Course and Internship Stands Out
See exactly what separates EasyShiksha students from everyone else
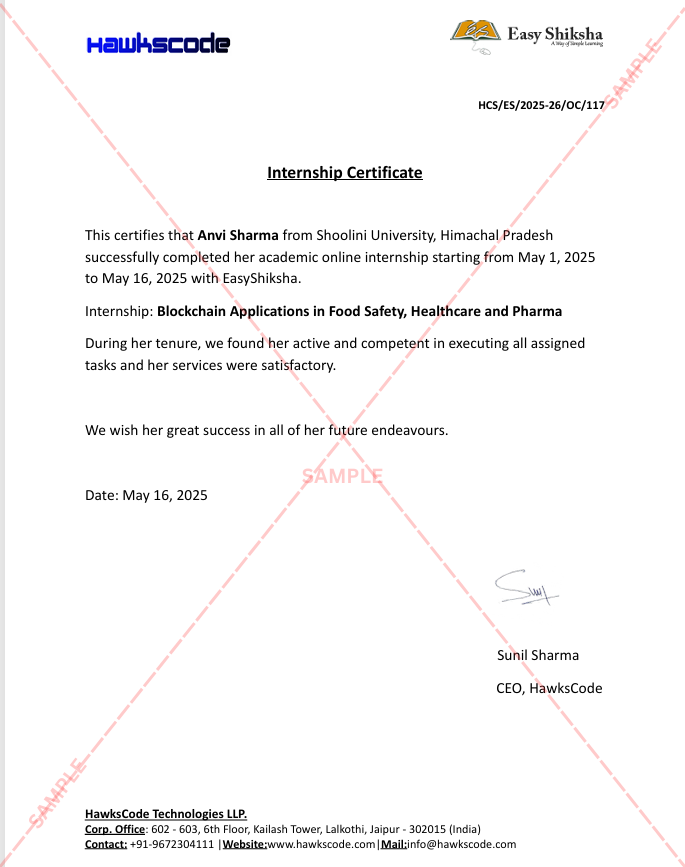
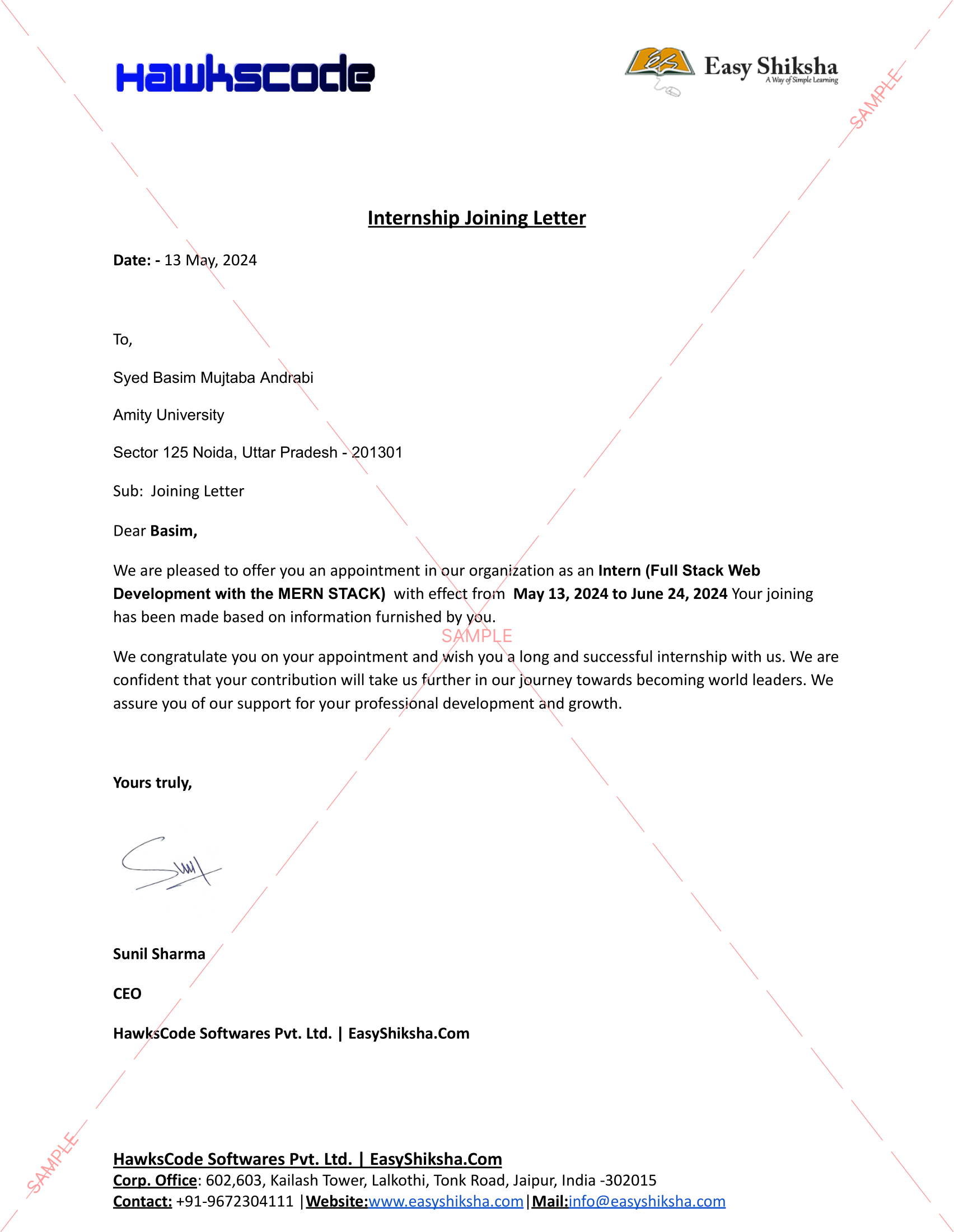
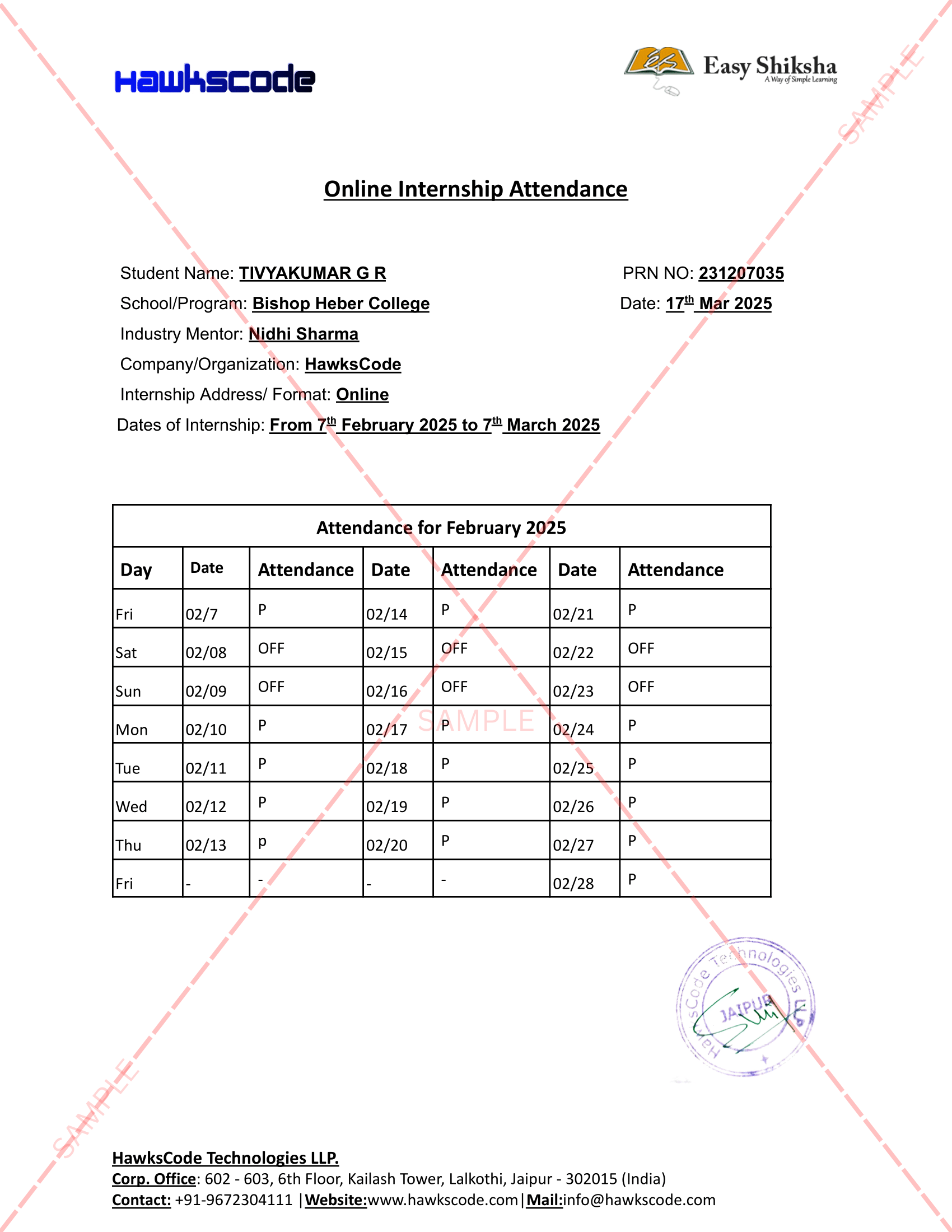
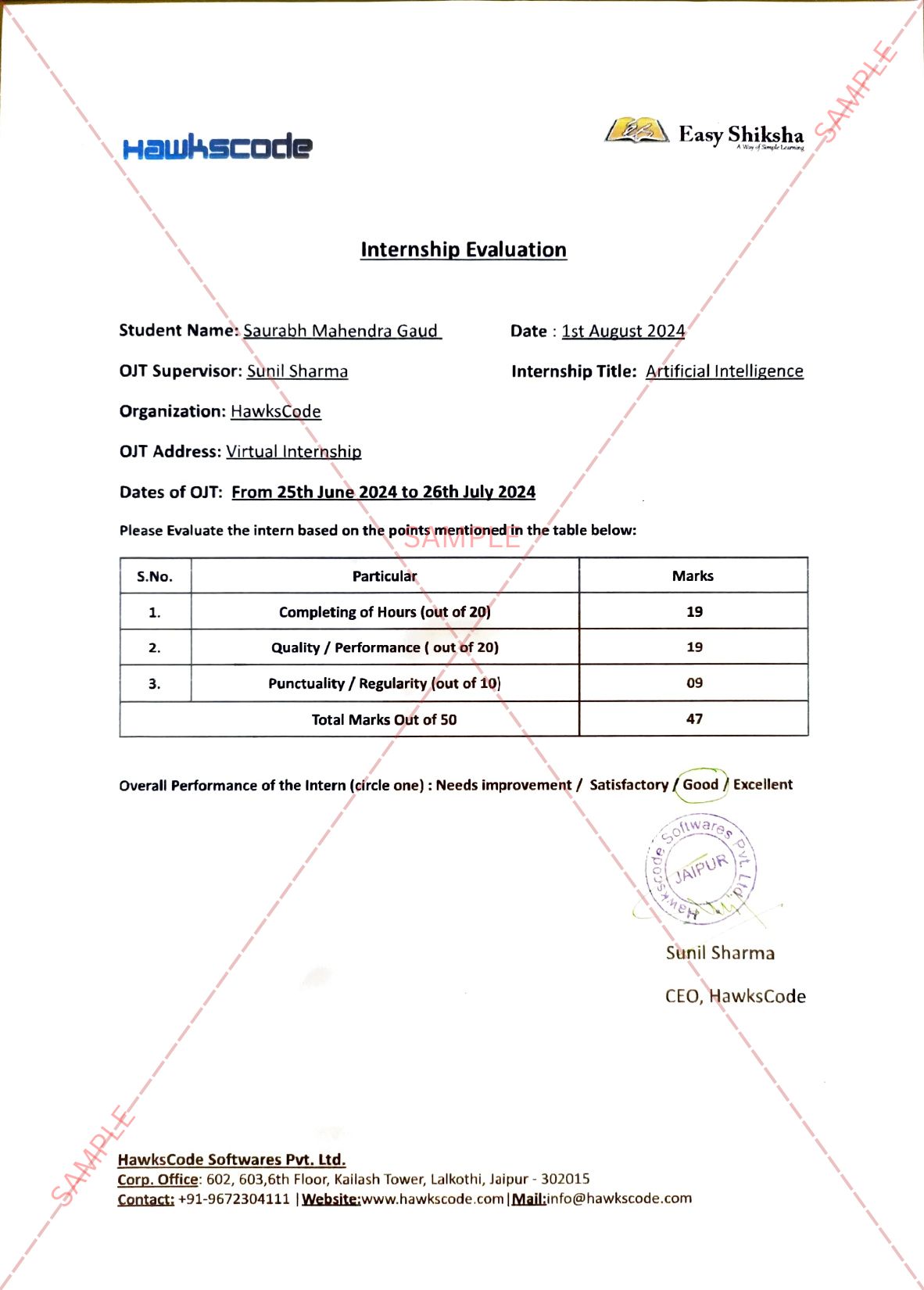
Internship Opportunity Included With This Course
"This is not just a course — it's real career experience. Walk away with documents that prove your skills to any employer."
This Course is Perfect For
Whether you're starting from scratch or switching careers — this course is designed with your success in mind.
This course uses elements of Artificial IntelligenceIn today’s digital-first world, identity is the new perimeter. Every user, device, and organizational boundary is under constant threat from increasingly sophisticated cyber adversaries. One weak link in your identity architecture can become a gateway to widespread breaches, catastrophic financial losses, and irreparable brand harm. How confident are you that your organization’s identity foundations—its architecture, governance, and protection mechanisms—can withstand the pressures of both today’s relentless attacks and tomorrow’s evolving landscapes?
Welcome to “Mastering Enterprise Identity Architecture: Security, Trust, and Organizational Resilience”—the most comprehensive, up-to-date course for IT professionals, architects, security leaders, and technologists determined to take control of identity in the enterprise. Designed and delivered by our experienced team of identity architects, global security consultants, and organizational advisors, this course does more than teach; it guides, challenges, and equips you to build, operate, and defend modern identity systems at scale.
Why Is Identity Architecture the Unshakeable Pillar of Enterprise Security?
The modern enterprise grapples with sprawling workforces, globally distributed teams, myriad devices, mergers, and the limitless complexity of cloud adoption. Meanwhile, adversaries exploit trust relationships, latent privileges, and fragmented identity controls to traverse and compromise organizations from within. As regulatory scrutiny intensifies and business needs shift overnight, only a strategically designed identity architecture can mitigate risk, sustain compliance, and foster agility.
What Makes This Course Essential—And Unique?
Unlike fragmented webinars, product-centric trainings, or how-to guides that focus narrowly on tooling, this course offers an end-to-end exploration of *enterprise identity as a discipline*. It is a fusion of engineering best practices, security strategy, real-world case analyses, and practical design labs—spanning the classic (such as Active Directory and role-based models) and the modern (including cloud federation, Zero Trust, and ethical considerations). From foundational building blocks to the cutting edge of biometrics, automation, and decentralized frameworks, we take you on a skills-building journey that will elevate your understanding and transform your career.
What Awaits You on This Journey?
You begin by demystifying the core elements of identity in the organizational context. Through hands-on labs and scenario-based exploration, you will see how user, group, and resource definitions govern policy, access, and visibility. Together, we’ll break down the abstract into the tangible—mapping centralized identity to real-world governance, and dissecting the critical factors that make or break enterprise security. Case studies grounded in modern organizations reveal both best-in-class models and the frequent, costly mistakes.
Taking the leap into Active Directory, you’ll trace its evolution as the de facto identity backbone. Our team’s multi-decade experience empowers you to see not just the ‘how’ but the ‘why’ behind directory services, policy mapping, authentication, and authorization. You’ll work through adoption stories that expose the architecture’s strengths—and learn where and how to apply it in hybrid, cloud-integrated environments.
As we delve deeper, you’ll acquire mastery over directory information models—objects, attributes, and schemas. You will visualize how forests, trees, and domains provide both structure and strategic isolation, and analyze how trust boundaries and delegated permissions fortify or weaken an organization’s security posture. Through practical, guided labs, you’ll manage identity lifecycles, building automated processes that minimize administrative risk while supporting dynamic organizational needs.
Navigate the Complexity—Securely and at Scale
The heart of the course lies in tackling the *messy reality* of enterprise scale. As organizations merge, grow, and reconfigure, identity architectures must adapt—often under pressure. You’ll get a front-row seat to real-world trust modeling, from one-way and two-way trusts to federated identity across cloud and partner boundaries. We don’t shy away from the “hard parts”: you’ll learn to defend against privilege escalation, minimize attack surfaces through least privilege, and construct fine-grained, policy-driven access controls suited to evolving regulatory requirements.
To cement your expertise, our course integrates active case studies and portfolio-ready projects at every stage. You will respond to simulated audit failures, spearhead access reviews, and design secure onboarding and offboarding workflows—experiencing firsthand the risk, tension, and triumph of building resilient systems. These aren’t mere exercises: they are reflective of real incidents, organizational expansions, mergers, insider threat scenarios, and regulatory changes. By the end, you will have deployed access governance models, architected security baselines, and managed identity migrations as part of a simulated global enterprise.
Dive into Modern and Emerging Controls
With the rapid evolution of threats, password-based security is no longer enough. You’ll master the transition to multi-factor authentication, adaptive conditional access policies, and contextual device trust—learning to mitigate credential theft with both policy and cutting-edge technology. Through global case studies, our instructors will draw from deployment experience in Fortune 500 and multinational firms, allowing you to understand not only best practice—but also the nuanced decisions and trade-offs that set world-class identity security apart.
We also tackle the critical challenges of hybrid identity: synchronizing directories, federating identity across public clouds, and navigating the seamless yet secure integration of on-premises and cloud-based services. You will architect business continuity solutions, streamline disaster recovery, and audit for compliance under real regulatory regimes—including SOX, GDPR, and emerging privacy standards. Practical, hands-on labs let you work with synchronization tools, federation protocols, and forensics frameworks—building confidence and capability that you can demonstrate in any organization.
Position Yourself for Leadership—And the Future
As identity remains a dynamic, board-level concern, the ability to communicate architectural value and risk to business stakeholders is paramount. Our instructors provide proven frameworks for aligning identity investments with organizational mission, quantifying risk, and presenting roadmaps that secure buy-in for long-term initiatives. You will develop strategic planning skills, learning to balance agility and resilience through policy and technical controls. We’ll arm you with templates, communication guides, and actionable strategies for influencing culture—so you can sustain identity stewardship as organizations evolve.
No course would be complete without tackling transformative trends. We unlock the potential (and pitfalls) of biometrics, machine learning, decentralized identity models, and the future of trust in the era of blockchain and beyond. These forward-looking modules are interwoven with speculative case studies, ensuring you not only stay current but also gain a first-mover advantage as the field develops.
Human Impact, Ethics, and the Organizational Soul
True mastery of identity architecture extends beyond technology. We provide grounding in privacy, ethics, and the human factors that shape security outcomes. You’ll build a nuanced appreciation for transparency, redress mechanisms, and people-driven risk—learning to balance accessibility with the constitutional right to data protection. Insider risk, organizational change, and the psychological toll of access decisions are explored with depth and honesty, empowering you to architect environments that respect and enable the enterprise’s most valuable asset: its people.
Your Learning Tools: Projects, Assessments, and Career Outcomes
- Hands-on labs in directory modeling, trust configuration, and access reviews.
- Real-world capstones that challenge you to design, defend, and recover identity architectures in high-pressure scenarios.
- Portfolio-ready deliverables: security baselines, policy frameworks, audit responses, disaster plans, and next-gen identity blueprints.
- Reflective exercises and instructor feedback to sharpen both technical and communication skills.
- Complex scenario-based quizzes and knowledge checks to ensure depth and retention at every stage.
Who Will You Become?
By the journey’s end, you won’t just understand enterprise identity—you’ll *own* it. Whether your ambition is to serve as a trusted security architect, lead global identity migrations, champion Zero Trust initiatives, or steer compliance in regulated industries, this course will accelerate your growth. You’ll acquire immediately-applicable knowledge in enterprise identity management, directory services, auditing, compliance, and organizational change—skills in the highest demand across cybersecurity, IT operations, and governance domains.
Setting You Apart in a Crowded Field
This course is the culmination of decades of enterprise identity engineering and leadership. Our team distills hard-earned wisdom from global deployments, regulatory audits, and security incident response into every module. You learn not only how to use the tools, but why design choices matter for organizational destiny. The blending of traditional directory expertise, cloud and hybrid best practices, futuristic trust models, and mature leadership lessons makes this course a singular, unmissable investment in your career.
Start Building the Foundations of Secure Digital Trust Today
Are you ready to transform your understanding of identity into a strategic, career-defining asset? Enrollment will grant you access to not just technical content, but a mentor-led learning community that empowers you to ask questions, tackle challenges, and deploy with confidence. No matter where you begin, you’ll finish equipped to safeguard organizations, influence stakeholders, and pave the road to resilient, ethical, and future-ready enterprise identity.
Secure your spot and join us in shaping the next era of trust. Your organization’s future—and your professional legacy—begin here.
Why Start Now?
The Opportunity Won’t Wait.
Every day you delay is a missed opportunity to grow your skills. Learners who start today gain the advantage — whether it's building skills, improving careers, or unlocking new opportunities.
Still Thinking?
Here's everything that makes this a no-brainer:
What Happens After You Enroll?
From payment to certificate — here's exactly what to expect
Imagine After Completing This Course
Picture yourself 30 days from now — with skills, experience, and credentials that open real doors.